Wi-fi data collection
Allegations about airport surveillance by the CSEC are hard to prove because so much is shrouded in secrecy.
Recent revelations about the Canadian Government's top-secret program that captured travellers data at Canadian airports has some wondering about the "broad umbrella" given to Canadian spies under Canadian law.
CBC broke the news in January, thanks to some leaked documents from ex-NSA contractor Edward Snowden, that Communications Security Establishment Canada (CSEC) was operating a program in Canadian airports that would capture the metadata of any user who logged onto the wi-fi. CSEC insisted that the program was supposed to test and improve the software, which they were designing for the Americans, and was never intended to capture the data of Canadians -- something, they reminded the public, that falls outside their mandate and would be illegal.
Yet those in the legal community who follow lawful access issues aren't taking CSEC's word for it.
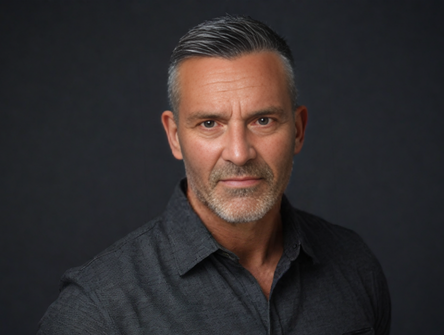
Michael Geist is a professor at the University of Ottawa, where he's the Canada Research Chair in Internet and E-commerce Law. He is one of those with concerns.
"First off, so much of this remains shrouded in secrecy. There is a real black block around, not just what is being done, but how it is being done," Geist told National.
Much of that mystery comes from the very nature of how CSEC is allowed to collect data.
Section 273.65 of the National Defence Act gives the Minister of National Defence the power to authorize private communications. The only stipulations? That the information cannot be otherwise obtained through regular methods, the information obtained must be of considerable value, it must respect Canadians privacy, and it cannot be targeted at Canadians directly.
The government has been quick to highlight that the secretive information-gathering courts that approve the NSA's requests to surveil Americans, the ones that many have underlined as emblematic of the problems with the American system, do not exist in Canada.
Though the system created by the ministerial order may, in fact, have less oversight.
"Rather than obtaining a specific court order... they're adopting a very broad umbrella that covers the capturing and access to metadata," says Geist.
The first ministerial authorization on metadata was made in 2005 and renewed in 2011. Given that it's been used consistently since then, it's unclear if the conditions set out in the act are being respected, seeing as how the only oversight for the secretive program comes by way of the commissioner for CSEC, who is tasked with evaluating the legality of CSEC's surveillance. Two commissioners have thus far given the thumbs-up to the organization's metadata-capturing programs.
But there are still questions over just how CSEC treats the data, how long they're allowed to retain it, and about what the commissioner considers legal under the act.
While the first ministerial authorization on metadata collection was signed by the Liberals, the current Conservative government has been specifically interested in facilitating access to metadata. Under the guise of their cyberbullying bill, C-13, they're aiming to lessen evidentiary thresholds needed for police to obtain production orders for metadata. The bill would also provide immunity to any digital information-holder who shares that digital data with law enforcement.
It's currently unclear, and will become even less clear when C-13 passes, if CSEC can provide the Justice Department or law enforcement with information obtained under the metadata-capturing program.
"I think there are people who would argue that it's already being improperly used," says Geist.
When National put the question to CSEC, a spokesperson wrote in an emailed response that the organization targets foreign entities and that "domestic agencies do not have access to CSEC’s metadata" but would not elaborate.
CSEC did admit, however, that "given the complex and global nature of cyberspace and telecommunications, CSE may risk the incidental interception of the private communications of Canadians when directing our activities at a foreign target. This risk occurs because we have no way of knowing in advance or control who our foreign targets will communicate with."
The spokesperson did not address the issue of what CSEC would do with the metadata of Canadians captured in their airport exercise.
The spokesperson maintained CSEC respects the Privacy Act and the Charter.
One organization wasn't convinced of that, and challenged the entire premise that CSEC can collect data in such a way.
In October, the BC Civil Liberties Association filed notice of civil claim against the government, arguing that the metadata collection regime impugns Canadians' Charter protections against unreasonable search and seizure and their right to freedom of communication.
"Unaccountable and unchecked government surveillance presents a grave threat to democratic freedoms. We are deeply concerned that CSEC is gaining secret, illegal access to the private communications of ordinary Canadians, and there are no reasonable safeguards in place to monitor its activities," said Joseph Arvay, lawyer for the organization and a partner at Farris, in Vancouver, quoted in a press release from the launch of the lawsuit.
The lawsuit is the first of its kind against CSEC. Yet, given the clarity in the act and the classified nature of the organization's data-collection process, there is slim chance that the organization suit will get far -- unless Snowden can continue supplying information that CSEC's programs are crossing the line in capturing Canadians' personal information.
The BC organization is contesting the very of Section 273.65, but they're drawing particular attention to the practise that the airport wi-fi plan underlines.
"We simply say that all that -- both the collection itself and the retention, use and analysis of that metadata over time -- constitutes a breach of section eight of the Charter," says Caily DiPuma, counsel at the BC Civil Liberties Association.
The Attorney General has moved to dismiss the claim, arguing both that the BC association does not have standing to challenge the provisions, as they've not identified anyone who has had their privacy breached by CSEC.
Given that it's quite difficult to prove whether or not a secret security establishment has violated your data, the BC association is fighting to get more information to prove just that. In the process, because of the national security implications, they might end up in Federal Court to establish just what is admissible in the case.
Geist says this is the confounding part of the whole system -- it's not even clear what's legal.
"The whole program itself is shrouded in secrecy," he says. "Do we have, from a legal perspective, the right rules? And do we have enough oversight to ensure that they're being followed properly?"